The new lightweight stealer, distributed via underground forums and cracked software, demonstrates an important evolution in the stealth of commodity infostealing malware. The new lightweight stealer, distributed via underground forums and cracked software, demonstrates an important evolution in the stealth of commodity infostealing malware.
- AI-Powered Sign-up Fraud Is Scaling Fast darkreading
- Chinese TA415 Uses VS Code Remote Tunnels to Spy on U.S. Economic Policy Experts The Hacker [email protected] (The Hacker News)
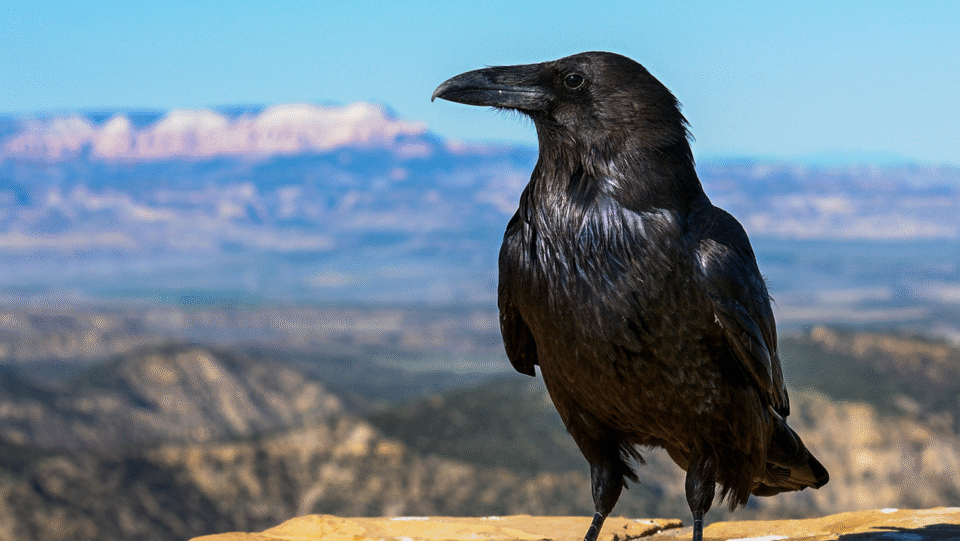
- Raven Stealer Scavenges Chromium Data Via Telegram darkreadingElizabeth Montalbano, Contributing Writer
- From Quantum Hacks to AI Defenses – Expert Guide to Building Unbreakable Cyber Resilience The Hacker [email protected] (The Hacker News)
- Rethinking AI Data Security: A Buyer’s Guide The Hacker [email protected] (The Hacker News)
- The Beginner’s Guide to Using AI: 5 Easy Ways to Get Started (Without Accidentally Summoning Skynet)by Tech Jacks
- Tips and Tricks to Enhance Your Incident Response Proceduresby Tech Jacks
- Building a Security Roadmap for Your Company: Strategic Precision for Modern Enterprises by Tech Jacks
- The Power of Policy: How Creating Strong Standard Operating Procedures Expedites Security Initiativesby Tech Jacks
- Building a Future-Proof SOC: Strategies for CISOs and Infosec Leaders by Tech Jacks
- Security Gate Keeping – Annoying – Unhelpfulby Tech Jacks
- The Beginner’s Guide to Using AI: 5 Easy Ways to Get Started (Without Accidentally Summoning Skynet)


Leave A Reply