This quick diary is a perfect example of why I love Linux (or UNIX in general) operating system. There is always a way to “escape” settings imposed by an admin…
This quick diary is a perfect example of why I love Linux (or UNIX in general) operating system. There is always a way to “escape” settings imposed by an admin…
Disclaimer: This has been used for testing purpose in the scope of a security assessment project. Don’t break your organization security policies!
To perform some assessments on a remote network, a Customer provided me a VM running Ubuntu and reachable through SSH (with IP filtering, only SSH key authentication, etc). Once logged on the system, I started to work but I was lacking of some tools and decided to install them. Bad news… The VM had no Internet access. No problem, we have an SSH access!
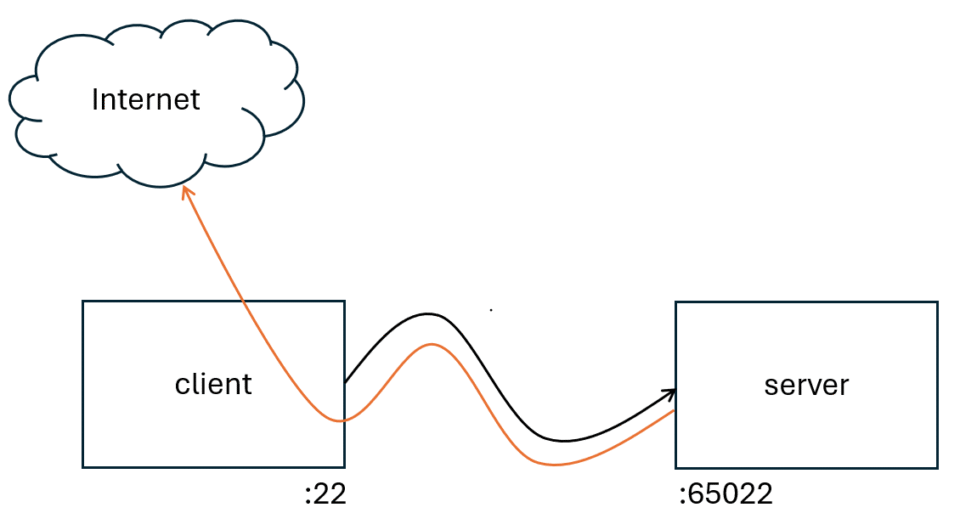
Let’s assume the following enrivonment:
- server.acme.org is the VM. SSH listening on port 65022.
- client.sans.edu is my workstation with SSH listening on port 22.
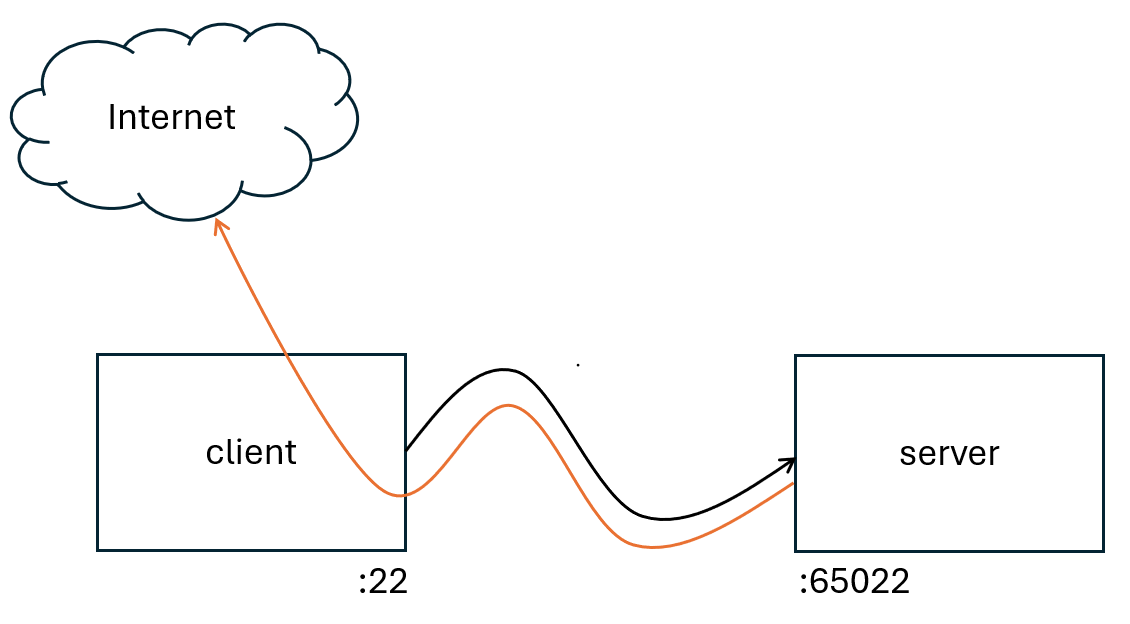
Step 1: From client.sans.edu, connect to the server via one terminal and create a reverse tunnel (“-R” option)
ssh -p 65022 -i .ssh/privatekey -R 2222:localhost:22 [email protected]
Step 2: Start a second session to the server, from a second terminal
ssh -p 65022 -i .ssh/privatekey [email protected]
Step 3: From the second session, connect back to the client and setup a dynamic port forwaring (“-D”)
ssh -p 2222 -D 1080 xavier@localhost
Step 4: From the fist session, create environment variables:
export http_proxy=socks5h://127.0.0.1:1080 export https_proxy=socks5h://127.0.0.1:1080 curl https://ipinfo.io/
Curl should tell you that your IP address is the one of client.sans.edu!
Now, all tools handling these variables will have access to the Interneet through your client! Slow but effective!
They are for sure many other ways to achieve this but… that’s the magic of UNIX, always plenty of way to solve issues… Please share your idea or techiques!
Xavier Mertens (@xme)
Xameco
Senior ISC Handler – Freelance Cyber Security Consultant
PGP Key
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.


Leave A Reply