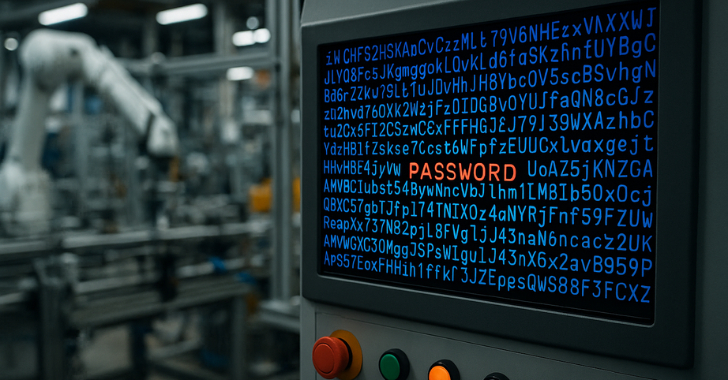
If you didn’t hear about Iranian hackers breaching US water facilities, it’s because they only managed to control a single pressure station serving 7,000 people. What made this attack noteworthy wasn’t its scale, but how easily the hackers gained access — by simply using the manufacturer’s default password “1111.” This narrow escape prompted CISA to urge manufacturers to If you didn’t hear about Iranian hackers breaching US water facilities, it’s because they only managed to control a single pressure station serving 7,000 people. What made this attack noteworthy wasn’t its scale, but how easily the hackers gained access — by simply using the manufacturer’s default password “1111.” This narrow escape prompted CISA to urge manufacturers to
- Interpol Arrests Over 1K Cybercriminals in ‘Operation Serengeti 2.0’ darkreadingKristina Beek
- Linux Malware Delivered via Malicious RAR Filenames Evades Antivirus Detection The Hacker [email protected] (The Hacker News)
- Apple Patches Zero-Day Flaw Used in ‘Sophisticated’ Attack darkreadingRob Wright
- The Growing Challenge of AI Agent and NHI Management darkreadingMichael Morgenstern
- Insurers May Limit Payments in Cases of Unpatched CVEs darkreadingRobert Lemos, Contributing Writer
- The Beginner’s Guide to Using AI: 5 Easy Ways to Get Started (Without Accidentally Summoning Skynet)by Tech Jacks
- Tips and Tricks to Enhance Your Incident Response Proceduresby Tech Jacks
- Building a Security Roadmap for Your Company: Strategic Precision for Modern Enterprises by Tech Jacks
- The Power of Policy: How Creating Strong Standard Operating Procedures Expedites Security Initiativesby Tech Jacks
- Building a Future-Proof SOC: Strategies for CISOs and Infosec Leaders by Tech Jacks
- Security Gate Keeping – Annoying – Unhelpfulby Tech Jacks
- The Beginner’s Guide to Using AI: 5 Easy Ways to Get Started (Without Accidentally Summoning Skynet)


Leave A Reply