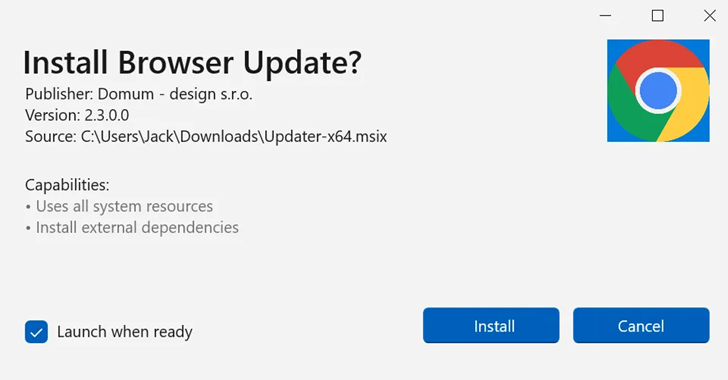
Bogus software update lures are being used by threat actors to deliver a new stealer malware called CoinLurker.
“Written in Go, CoinLurker employs cutting-edge obfuscation and anti-analysis techniques, making it a highly effective tool in modern cyber attacks,” Morphisec researcher Nadav Lorber said in a technical report published Monday.
The attacks make use of fake update alerts that employ Bogus software update lures are being used by threat actors to deliver a new stealer malware called CoinLurker.
“Written in Go, CoinLurker employs cutting-edge obfuscation and anti-analysis techniques, making it a highly effective tool in modern cyber attacks,” Morphisec researcher Nadav Lorber said in a technical report published Monday.
The attacks make use of fake update alerts that employ
- An Audit Isn’t a Speed Bump — It’s Your Cloud Co-Pilot darkreadingRavi Sharma
- Amazon Disrupts APT29 Watering Hole Campaign Abusing Microsoft Device Code Authentication The Hacker [email protected] (The Hacker News)
- Abandoned Sogou Zhuyin Update Server Hijacked, Weaponized in Taiwan Espionage Campaign The Hacker [email protected] (The Hacker News)
- Proof-of-Concept in 15 Minutes? AI Turbocharges Exploitation darkreadingRobert Lemos, Contributing Writer
- Can Your Security Stack See ChatGPT? Why Network Visibility Matters The Hacker [email protected] (The Hacker News)
- The Beginner’s Guide to Using AI: 5 Easy Ways to Get Started (Without Accidentally Summoning Skynet)by Tech Jacks
- Tips and Tricks to Enhance Your Incident Response Proceduresby Tech Jacks
- Building a Security Roadmap for Your Company: Strategic Precision for Modern Enterprises by Tech Jacks
- The Power of Policy: How Creating Strong Standard Operating Procedures Expedites Security Initiativesby Tech Jacks
- Building a Future-Proof SOC: Strategies for CISOs and Infosec Leaders by Tech Jacks
- Security Gate Keeping – Annoying – Unhelpfulby Tech Jacks
- The Beginner’s Guide to Using AI: 5 Easy Ways to Get Started (Without Accidentally Summoning Skynet)


Leave A Reply