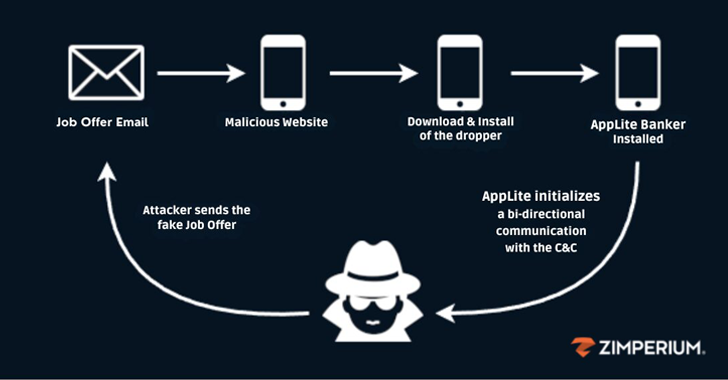
Cybersecurity researchers have shed light on a sophisticated mobile phishing (aka mishing) campaign that’s designed to distribute an updated version of the Antidot banking trojan.
“The attackers presented themselves as recruiters, luring unsuspecting victims with job offers,” Zimperium zLabs Vishnu Pratapagiri researcher said in a new report.
“As part of their fraudulent hiring process, the Cybersecurity researchers have shed light on a sophisticated mobile phishing (aka mishing) campaign that’s designed to distribute an updated version of the Antidot banking trojan.
“The attackers presented themselves as recruiters, luring unsuspecting victims with job offers,” Zimperium zLabs Vishnu Pratapagiri researcher said in a new report.
“As part of their fraudulent hiring process, the
- Hackers Turn Velociraptor DFIR Tool Into Weapon in LockBit Ransomware Attacks The Hacker [email protected] (The Hacker News)
- 1Password Addresses Critical AI Browser Agent Security Gap darkreadingArielle Waldman
- RondoDox Botnet: an ‘Exploit Shotgun’ for Edge Vulns darkreadingNate Nelson, Contributing Writer
- The Fight Against Ransomware Heats Up on the Factory Floor darkreadingArielle Waldman
- Feds Shutter ShinyHunters Salesforce Extortion Site darkreadingKristina Beek
- The Beginner’s Guide to Using AI: 5 Easy Ways to Get Started (Without Accidentally Summoning Skynet)by Tech Jacks
- Tips and Tricks to Enhance Your Incident Response Proceduresby Tech Jacks
- Building a Security Roadmap for Your Company: Strategic Precision for Modern Enterprises by Tech Jacks
- The Power of Policy: How Creating Strong Standard Operating Procedures Expedites Security Initiativesby Tech Jacks
- Building a Future-Proof SOC: Strategies for CISOs and Infosec Leaders by Tech Jacks
- Security Gate Keeping – Annoying – Unhelpfulby Tech Jacks
- The Beginner’s Guide to Using AI: 5 Easy Ways to Get Started (Without Accidentally Summoning Skynet)


Leave A Reply