Sextortion e-mails have been with us for quite a while, and these days, most security professionals tend to think of them more in terms of an âe-mail background noiseâ rather than as if they posed any serious threat. Given that their existence is reasonably well-known even among general public, this viewpoint would seem to be justified⦠But are sextortion messages really irrelevant as a threat at this point, and can we therefore safely omit this topic during security awareness trainings?
Sextortion e-mails have been with us for quite a while, and these days, most security professionals tend to think of them more in terms of an “e-mail background noise” rather than as if they posed any serious threat. Given that their existence is reasonably well-known even among general public, this viewpoint would seem to be justified… But are sextortion messages really irrelevant as a threat at this point, and can we therefore safely omit this topic during security awareness trainings?
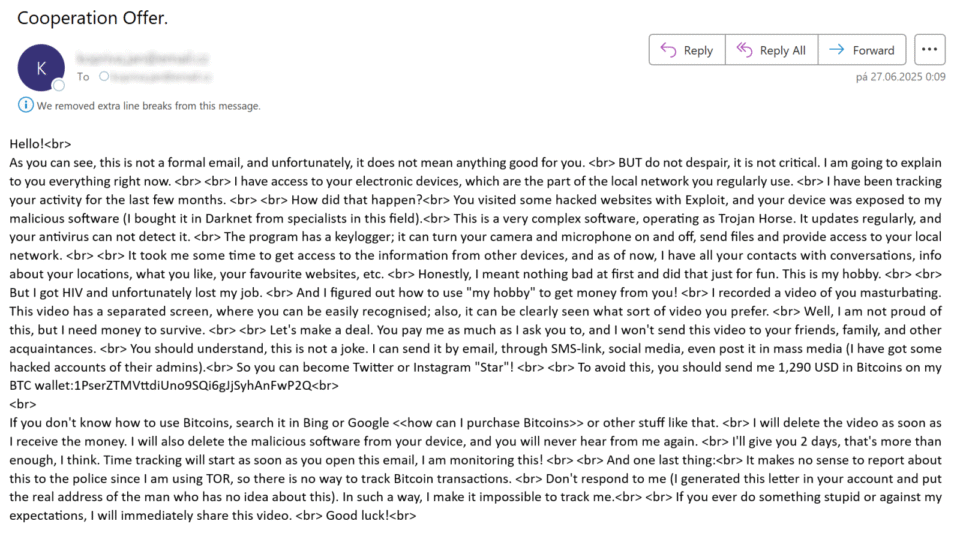
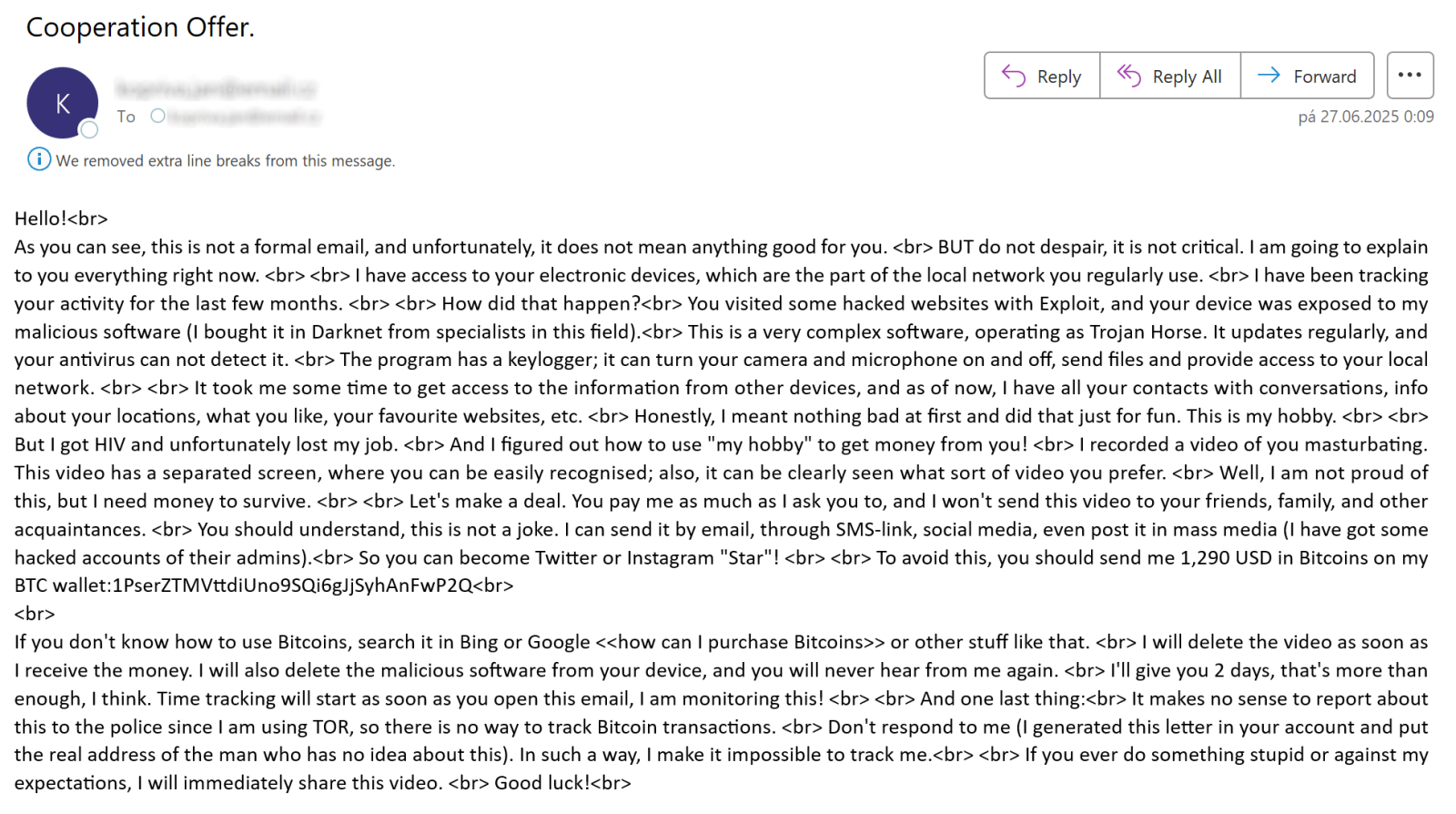
I thought that it might be worthwhile to try and find out, so I decided to go over sextortion messages that were delivered to my various spam traps and e-mail accounts during the past 12 months and see whether the cryptocurrency addresses mentioned in them actually received any payments.
In total, I collected 21 different e-mail messages that asked for payment to be sent to 15 distinct cryptocurrency addresses (13 of these were Bitcoin addresses and 2 were Litecoin addresses). For completeness’s sake, it should be noted that while most of the addresses were only seen in e-mails delivered during a single day, this wasn’t always the case, as one of the addresses was observed in messages sent out 32 days apart.
Admittedly, 15 addresses represent a rather small sample size, but it proved to be more than sufficient to give us the desired information about the continued effectiveness of sextortion…
In the sextortion messages, their senders were asking for payments of between $750 and $1,550, with average and median requested amounts being $1,203 and $1,250, respectively. While 6 of the 15 identified addresses didn’t receive any payments at all, the remaining 9 did – in total, incoming transactions to these addresses amounted to between $945 and $10,715, with average and median total amounts received being $1,836 and $1,028, respectively.
Although not all incoming payments to the addresses were necessarily connected solely to sextortion, it seems highly probable that at least most of them were… Which suggests that even in 2025, sextortion is still a relevant threat, and a topic that warrants attention in security awareness programs.
———–
Jan Kopriva
LinkedIn
Nettles Consulting
(c) SANS Internet Storm Center. https://isc.sans.edu Creative Commons Attribution-Noncommercial 3.0 United States License.


Leave A Reply