The cybersecurity landscape has been dramatically reshaped by the advent of generative AI. Attackers now leverage large language models (LLMs) to impersonate trusted individuals and automate these social engineering tactics at scale.
Let’s review the status of these rising attacks, what’s fueling them, and how to actually prevent, not detect, them.
The Most Powerful Person on the The cybersecurity landscape has been dramatically reshaped by the advent of generative AI. Attackers now leverage large language models (LLMs) to impersonate trusted individuals and automate these social engineering tactics at scale.
Let’s review the status of these rising attacks, what’s fueling them, and how to actually prevent, not detect, them.
The Most Powerful Person on the
- China-Linked APTs Exploit SAP CVE-2025-31324 to Breach 581 Critical Systems Worldwide The Hacker [email protected] (The Hacker News)
- Malicious PyPI Package Posing as Solana Tool Stole Source Code in 761 Downloads The Hacker [email protected] (The Hacker News)
- DeepSeek, Deep Research Mean Deep Changes for AI Security darkreadingLiam Crilly
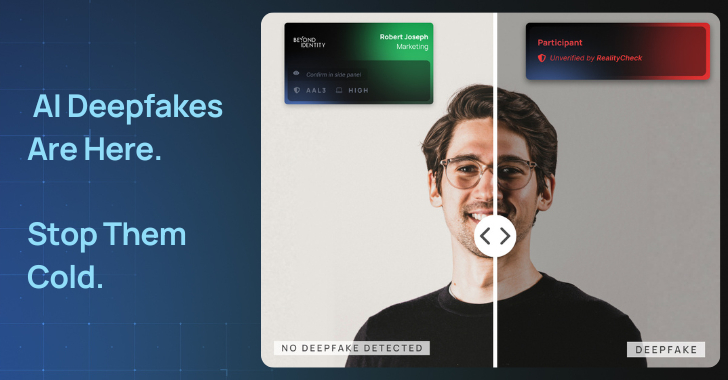
- Deepfake Defense in the Age of AI The Hacker [email protected] (The Hacker News)
- North Korean Konni APT Targets Ukraine with Malware to track Russian Invasion Progress The Hacker [email protected] (The Hacker News)
- The Beginner’s Guide to Using AI: 5 Easy Ways to Get Started (Without Accidentally Summoning Skynet)by Tech Jacks
- Tips and Tricks to Enhance Your Incident Response Proceduresby Tech Jacks
- Building a Security Roadmap for Your Company: Strategic Precision for Modern Enterprises by Tech Jacks
- The Power of Policy: How Creating Strong Standard Operating Procedures Expedites Security Initiativesby Tech Jacks
- Building a Future-Proof SOC: Strategies for CISOs and Infosec Leaders by Tech Jacks
- Security Gate Keeping – Annoying – Unhelpfulby Tech Jacks
- The Beginner’s Guide to Using AI: 5 Easy Ways to Get Started (Without Accidentally Summoning Skynet)


Leave A Reply