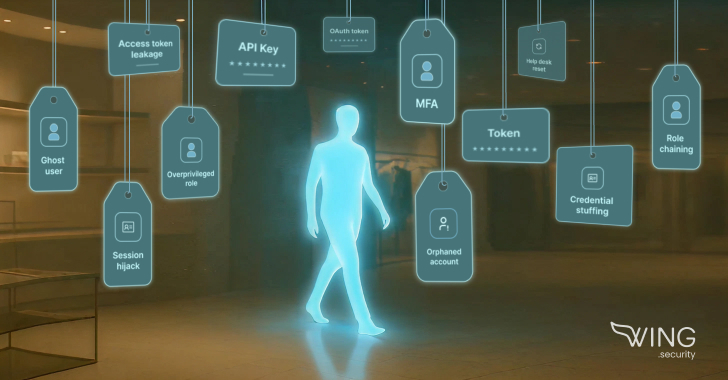
From overprivileged admin roles to long-forgotten vendor tokens, these attackers are slipping through the cracks of trust and access. Here’s how five retail breaches unfolded, and what they reveal about…
In recent months, major retailers like Adidas, The North Face, Dior, Victoria’s Secret, Cartier, Marks & Spencer, and Co‑op have all been breached. These attacks weren’t sophisticated From overprivileged admin roles to long-forgotten vendor tokens, these attackers are slipping through the cracks of trust and access. Here’s how five retail breaches unfolded, and what they reveal about…
In recent months, major retailers like Adidas, The North Face, Dior, Victoria’s Secret, Cartier, Marks & Spencer, and Co‑op have all been breached. These attacks weren’t sophisticated
- Linux Malware Delivered via Malicious RAR Filenames Evades Antivirus Detection The Hacker [email protected] (The Hacker News)
- Apple Patches Zero-Day Flaw Used in ‘Sophisticated’ Attack darkreadingRob Wright
- The Growing Challenge of AI Agent and NHI Management darkreadingMichael Morgenstern
- Insurers May Limit Payments in Cases of Unpatched CVEs darkreadingRobert Lemos, Contributing Writer
- Do Claude Code Security Reviews Pass the Vibe Check? darkreadingEricka Chickowski, Contributing Writer
- The Beginner’s Guide to Using AI: 5 Easy Ways to Get Started (Without Accidentally Summoning Skynet)by Tech Jacks
- Tips and Tricks to Enhance Your Incident Response Proceduresby Tech Jacks
- Building a Security Roadmap for Your Company: Strategic Precision for Modern Enterprises by Tech Jacks
- The Power of Policy: How Creating Strong Standard Operating Procedures Expedites Security Initiativesby Tech Jacks
- Building a Future-Proof SOC: Strategies for CISOs and Infosec Leaders by Tech Jacks
- Security Gate Keeping – Annoying – Unhelpfulby Tech Jacks
- The Beginner’s Guide to Using AI: 5 Easy Ways to Get Started (Without Accidentally Summoning Skynet)


Leave A Reply