China-Linked Hackers Launch Targeted Espionage Campaign on African IT Infrastructure The Hacker [email protected] (The Hacker News)
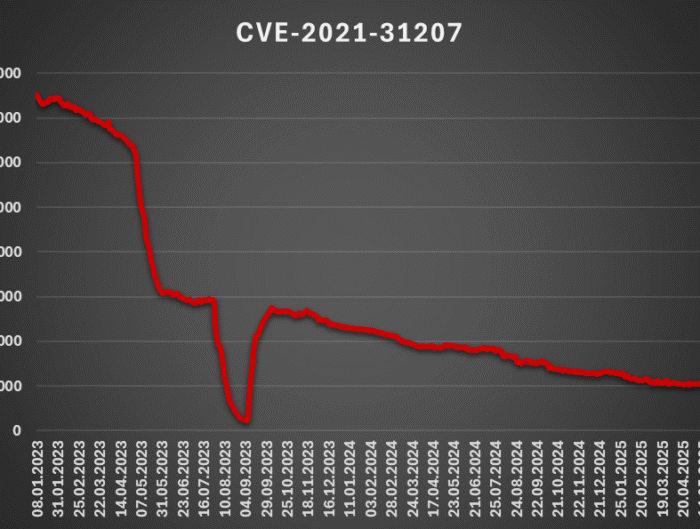
The China-linked cyber espionage group tracked as APT41 has been attributed to a new campaign targeting government IT services in the African region. "The attackers used hardcoded names of internal services, …