ScarCruft Uses RokRAT Malware in Operation HanKook Phantom Targeting South Korean Academics The Hacker [email protected] (The Hacker News)
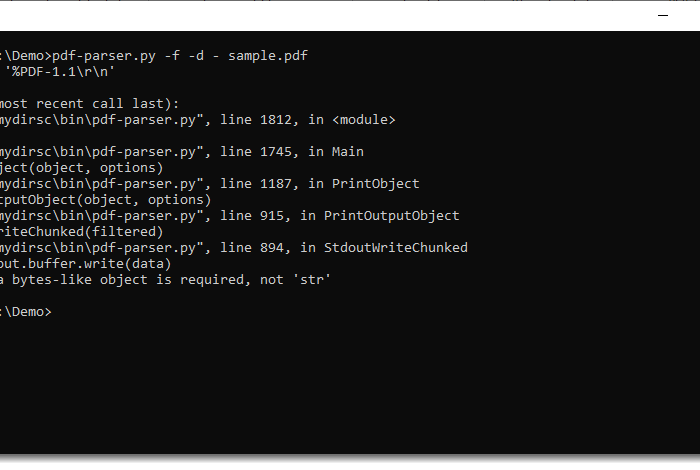
Cybersecurity researchers have discovered a new phishing campaign undertaken by the North Korea-linked hacking group called ScarCruft (aka APT37) to deliver a malware known as RokRAT. The activity has been codenamed …