Silver Fox Exploits Microsoft-Signed WatchDog Driver to Deploy ValleyRAT Malware The Hacker [email protected] (The Hacker News)
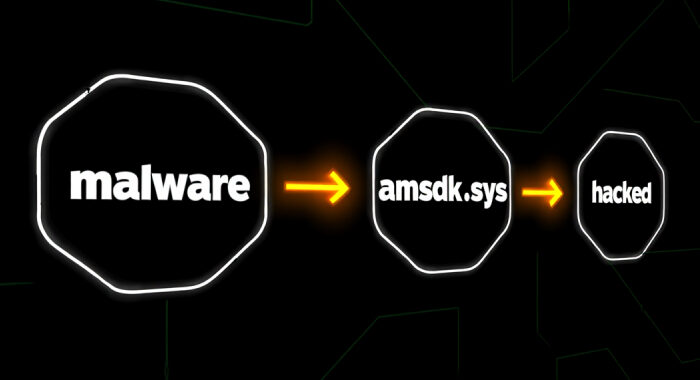
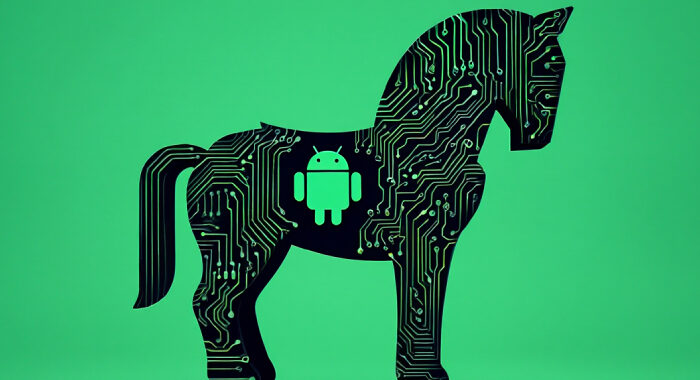
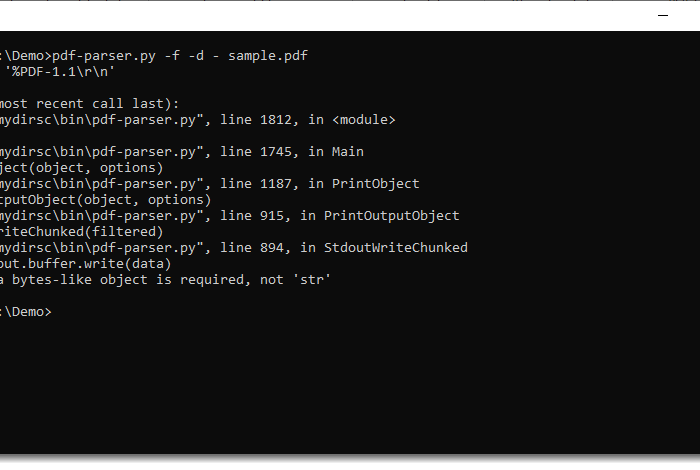
The threat actor known as Silver Fox has been attributed to abuse of a previously unknown vulnerable driver associated with WatchDog Anti-malware as part of a Bring Your Own Vulnerable …