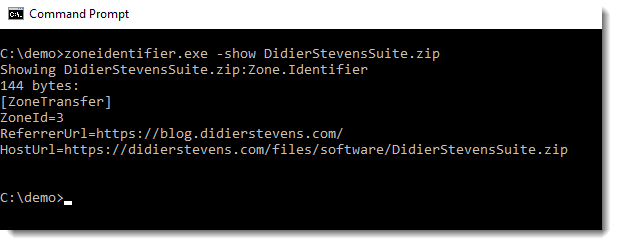
CISA Releases Nine Industrial Control Systems Advisories AlertsCISA
CISA released nine Industrial Control Systems (ICS) advisories on July 22, 2025. These advisories provide timely information about current security issues, vulnerabilities, and exploits surrounding ICS. ICSA-25-203-01 DuraComm DP-10iN-100-MU ICSA-25-203-02 Lantronix Provisioning …