DragonForce Ransom Cartel Profits Off Rivals’ Demise darkreadingAlexander Culafi
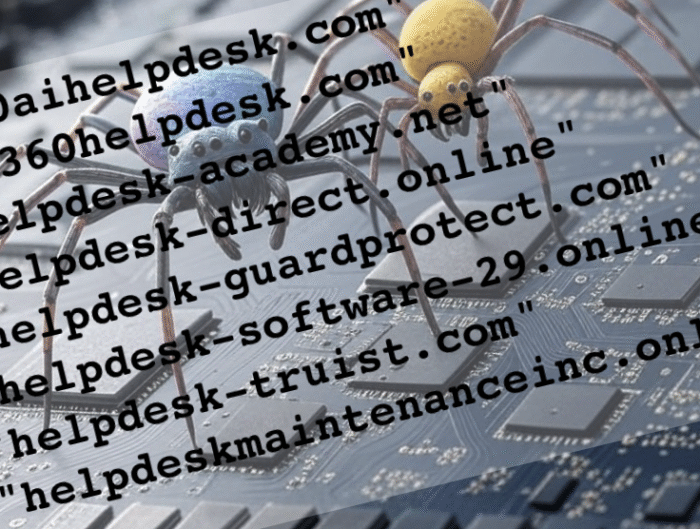
The fall of RansomHub led to a major consolidation of the ransomware ecosystem last quarter, which was a boon for the DragonForce and Qilin gangs. The fall of RansomHub led to …