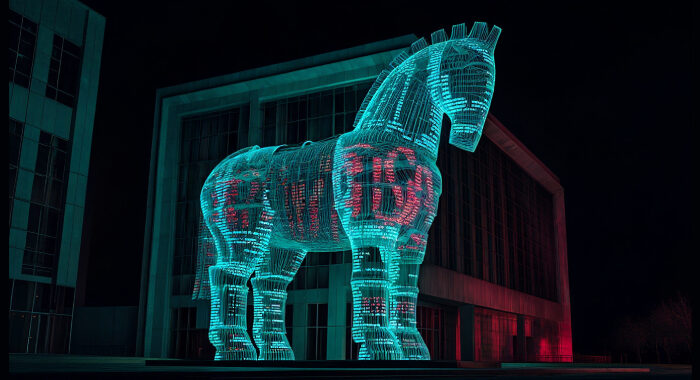
Salesloft OAuth Breach via Drift AI Chat Agent Exposes Salesforce Customer Data The Hacker [email protected] (The Hacker News)
A widespread data theft campaign has allowed hackers to breach sales automation platform Salesloft to steal OAuth and refresh tokens associated with the Drift artificial intelligence (AI) chat agent. The activity, …